
In 2022, cross chain bridges accounted for 69% of all cryptocurrency stolen that year. Hackers drained over $2 billion from these protocols alone, making bridges the single most dangerous category of infrastructure in decentralized finance.
The math explains why. Bridges hold massive pools of locked assets that back wrapped tokens on other blockchains. A successful attack against one bridge can yield hundreds of millions in a single transaction. For sophisticated threat actors, including state sponsored hackers from North Korea, bridges represent the highest value targets in the entire crypto ecosystem.
Ethereum co founder Vitalik Buterin had long warned about the fundamental security limits of cross chain bridges. On January 7, 2022, he published a detailed explanation of why bridges create systemic risk: a 51% attack on one chain could theoretically compromise assets locked across multiple networks. The exploits that followed in 2022 came from different vulnerabilities, but proved his broader point about bridge fragility. Compromised private keys enabled the Ronin and Harmony hacks. Smart contract bugs destroyed Wormhole and Nomad. Together, these four attacks resulted in over $1.2 billion stolen, with Ronin alone losing $624 million in what remains the largest DeFi hack in history.
The four bridge exploits that dominated 2022 share a troubling pattern. Each attack exploited known vulnerability types. Each could have been prevented with better security practices. And each left users with little to no recourse for recovering their funds.
Understanding how these attacks happened is the first step toward not becoming the next victim. The Ronin hack began with something as simple as a job offer on LinkedIn.
In late 2021, a senior engineer at Sky Mavis received a message on LinkedIn. A recruiter from what appeared to be a legitimate company was offering an exciting opportunity. After multiple rounds of interviews, the engineer received an offer letter as a PDF attachment. Opening that file deployed spyware that would eventually enable the largest hack in DeFi history.
Sky Mavis operated the Ronin Network, an Ethereum sidechain built specifically for Axie Infinity, a blockchain game that at its peak had 2.7 million daily active users. The Ronin Bridge allowed players to move assets between Ethereum and the game. Security depended on 9 validator nodes, with any 5 required to approve withdrawals.
The attackers, later identified as North Korea's Lazarus Group, used the compromised engineer's access to penetrate Sky Mavis infrastructure. They gained control of four validator keys belonging to the company. But they still needed a fifth.
They found it through a security oversight from months earlier. In November 2021, Axie DAO had temporarily granted Sky Mavis permission to sign transactions on its behalf during a period of heavy network load. When the arrangement ended in December, the access was never revoked. The attackers discovered this forgotten permission and used it to obtain the fifth signature they needed.
On March 23, 2022, the attackers executed two transactions that drained 173,600 ETH and 25.5 million USDC from the Ronin Bridge. The total value exceeded $624 million.
Nobody noticed for six days.
The breach was only discovered on March 29 when a user tried to withdraw 5,000 ETH and the transaction failed. Sky Mavis had no monitoring system in place to flag large outflows. By the time they realized what had happened, the attackers had already begun moving funds through Tornado Cash.
The FBI publicly attributed the attack to Lazarus Group on April 14, 2022. Recovery efforts retrieved approximately $36 million, just 6% of the total stolen. Sky Mavis raised $150 million from Binance and other investors to reimburse affected users, but the damage to trust was permanent.
The Wormhole attack had happened just seven weeks earlier, proving that Ronin was not an isolated failure.
Seven weeks before Ronin fell, another bridge had already demonstrated how quickly hundreds of millions could vanish. On February 2, 2022, an attacker exploited a vulnerability in the Wormhole bridge to mint 120,000 wrapped ETH on Solana without depositing any collateral. The tokens were worth $326 million.
Wormhole connects multiple blockchains including Ethereum and Solana, allowing users to transfer assets between networks. The bridge relies on a group of validators called Guardians who verify that deposits on one chain are legitimate before minting equivalent tokens on another.
The attacker found a way to bypass this verification entirely. A function called load_instruction_at had been deprecated in Solana's codebase months earlier, but Wormhole's contracts still used it. The attacker exploited this outdated code to spoof a system account and trick the bridge into accepting fabricated Guardian signatures. Security researcher samczsun later explained that the attacker essentially forged approval from validators who never actually signed anything.
With fake signatures accepted, the attacker minted 120,000 wETH on Solana backed by nothing. They immediately began moving the stolen funds across chains.
The implications extended far beyond the direct theft. Wrapped ETH served as collateral across dozens of Solana DeFi protocols. If those tokens suddenly became worthless, lending platforms would face mass insolvency. The entire DeFi ecosystem risked collapse.
Within hours, Jump Crypto intervened. The trading firm, which had acquired Wormhole's developer Certus One months earlier, replaced the entire 120,000 ETH from its own reserves. The bailout restored the backing for wETH and prevented cascading failures across Solana.
Not every bridge would receive such rescue. When Nomad suffered its own exploit six months later, no single entity could save it. Instead, hundreds of strangers would race to drain whatever remained.
Paradigm security researcher samczsun called it "one of the most chaotic hacks that Web3 has ever seen." On August 1, 2022, the Nomad bridge lost $190 million not to a single sophisticated attacker, but to a feeding frenzy of over 300 separate addresses racing to drain whatever they could grab.
The vulnerability originated from a routine upgrade in June 2022. During the update, developers initialized a critical variable called the trusted root to 0x00, the zero address. This single configuration error had catastrophic consequences. The bridge's verification system used this root to confirm that withdrawal requests were legitimate. With 0x00 marked as trusted, every message was automatically considered valid.
The first attacker discovered this flaw and began draining funds. But unlike Ronin or Wormhole, exploiting Nomad required no technical expertise whatsoever. The attack transactions were public on the blockchain. Anyone could copy a successful withdrawal, replace the destination address with their own, and broadcast it. The bridge would approve it automatically.
Word spread through crypto Twitter and Discord within minutes. More than 300 addresses joined the looting over the next few hours. Security firm PeckShield estimated that 41 addresses captured 80% of the stolen funds, approximately $152 million. The remaining 20% was scattered among hundreds of smaller participants, some taking just a few thousand dollars each.
Not everyone who grabbed funds intended to keep them. Several white hat hackers recognized what was happening and withdrew assets specifically to protect them from malicious actors. These ethical participants later returned approximately $36 million to Nomad, about 20% of total losses. But many more white hats hesitated to intervene, fearing legal consequences for touching stolen funds. This gap in protection later inspired samczsun to create SEAL 911, a rapid response network of vetted security researchers who can now assist during active exploits without risking prosecution.
The incident earned nicknames like "decentralized robbery" and "crowd sourced looting." It demonstrated that bridge security failures could create opportunities for mass participation in theft, lowering the barrier from skilled hackers to anyone who could copy and paste.
The regulatory consequences arrived three years later. In December 2025, the FTC announced a proposed settlement against Nomad, alleging the company failed to implement reasonable security practices despite marketing itself as a "security first" platform. According to the complaint, Nomad lacked adequate unit testing, had no written security plan, employed insufficient security staff, and had no circuit breaker to halt the bridge during suspicious activity. When the exploit began, the team had to rely on an engineer who was on a plane to relay code snippets via chat. The bridge was not shut down until after it had been emptied. Of the $186 million stolen, approximately $100 million was never recovered.
Months earlier, a security researcher had publicly warned that another bridge was equally vulnerable. His prediction would prove accurate within 83 days.
On April 1, 2022, a security researcher using the handle @_apedev posted a thread on Twitter analyzing the Harmony Horizon Bridge. He noted that the bridge's security depended on a multisig wallet requiring only two of five signers to approve transactions. His conclusion was blunt: "if two of the four multisig signers are compromised, we're going to see another nine figure hack."

Exactly 83 days later, his prediction came true.
On June 23, 2022, attackers compromised two private keys and used them to drain $100 million from the Horizon Bridge. The theft required no sophisticated exploit, no code vulnerability, no social engineering campaign. The attackers simply obtained enough signatures to authorize withdrawals, and the bridge had set that threshold dangerously low.
The FBI confirmed in January 2023 that North Korea's Lazarus Group was responsible. The same organization behind Ronin had struck again, using similar techniques to compromise private keys. Within days of the theft, the attackers began laundering funds through Tornado Cash. After that mixer was sanctioned by the U.S. Treasury in August 2022, they switched to Railgun, a privacy protocol on Ethereum.
Harmony offered a $10 million bounty for information leading to fund recovery. The effort produced no meaningful results. Unlike Wormhole, no wealthy backer stepped in to make users whole. Unlike Nomad, there were no white hats returning stolen assets.
The Harmony hack crystallized a painful lesson. The warning signs had been public for months. A researcher had identified the exact vulnerability and predicted the outcome. Yet the bridge operators took no action to increase their signature threshold or improve key security.
Four bridges, four different attack vectors, and over $1.2 billion stolen in a single year. But these incidents shared common patterns that would repeat again and again.
The four exploits examined above represent different attack vectors, but they fall into predictable categories. Understanding these patterns helps identify which bridges carry the highest risk.
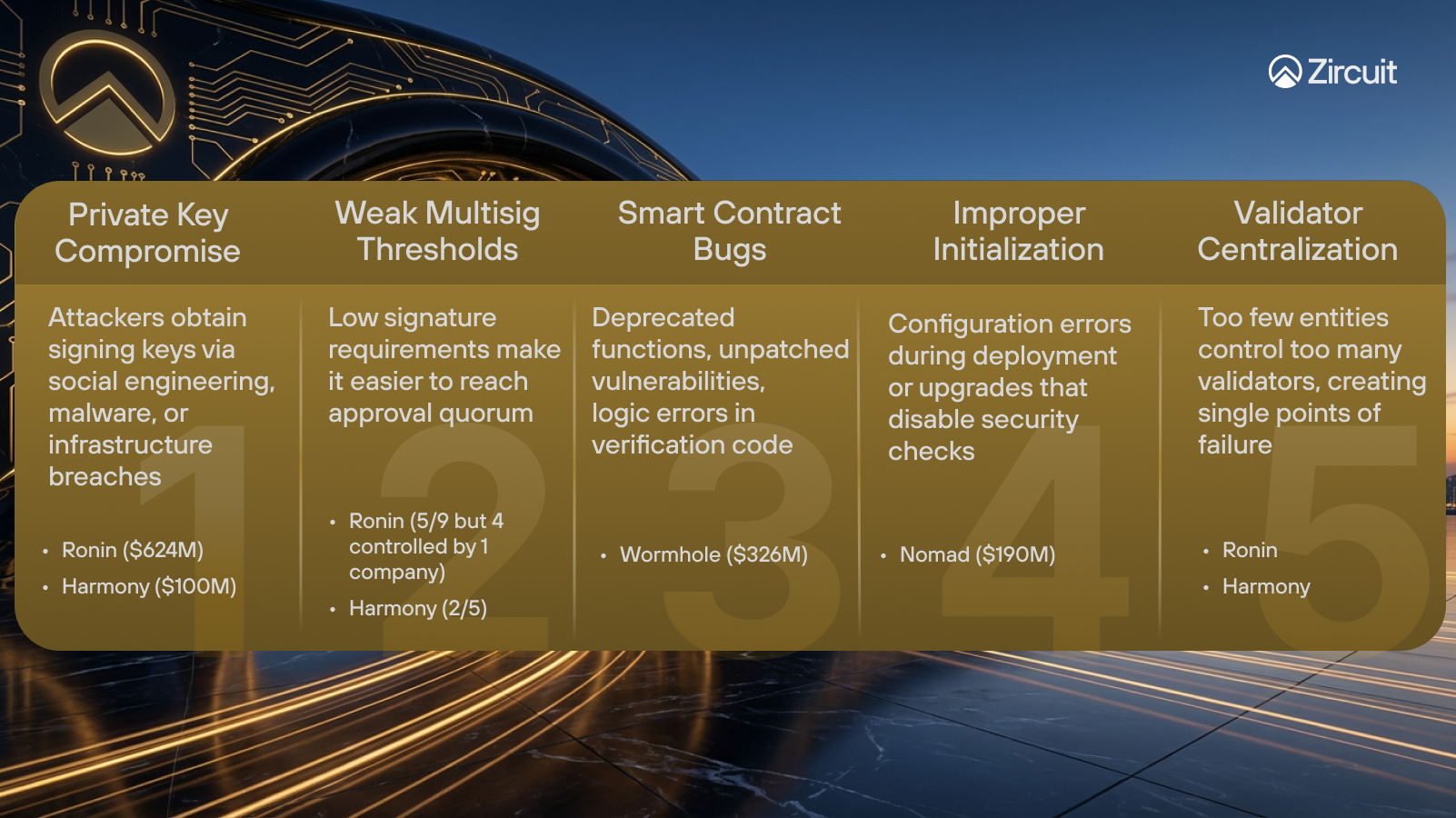
These vulnerabilities are not mutually exclusive. Many attacks combine multiple weaknesses. Ronin, for example, involved both private key compromise and validator centralization. Recognizing these patterns is the first step toward safer bridging practices.
No bridge is completely safe, but informed users can reduce their exposure. These practices address the specific vulnerabilities that enabled the attacks described above.
Evaluate the security architecture before bridging. Check how many validators or signers secure the bridge and what threshold is required to approve transactions. A 2 of 5 multisig is far weaker than 7 of 10. Research whether validators are controlled by independent organizations or concentrated under one entity. L2BEAT provides risk assessments for many popular bridges.
Prefer native bridges when moving significant amounts. Canonical bridges built directly into Layer 2 networks inherit security from Ethereum itself. The tradeoff is longer withdrawal periods, sometimes up to seven days, but the security model is stronger than third party validator sets.
Split large transfers across multiple transactions. If you need to move $10,000, consider ten separate transactions of $1,000 each. This limits exposure if an exploit occurs while your funds are in transit.
Revoke token approvals after bridging. Bridges often request unlimited spending permissions. Once your transfer completes, use tools like Revoke.cash to remove these approvals. Several exploits have targeted standing permissions from previous bridge interactions.
Wait for full finality on both chains. Transactions can succeed on the source chain but fail on the destination. Do not assume funds are safe until confirmations complete on both sides. You should look at the processing times of established exchanges like Kraken.
Check the bridge's track record. How long has it operated? Has it suffered previous exploits? Newer bridges have not been battle tested. History matters.
Four bridges. Four different attack methods. Over $1.2 billion stolen in 2022 alone. The Ronin hack began with a fake job offer. Wormhole fell to a deprecated function that should have been removed months earlier. Nomad collapsed because a routine upgrade accidentally disabled all security checks. Harmony ignored public warnings for 83 days until the predicted attack arrived.
These were not sophisticated zero day exploits. They were preventable failures rooted in weak security architecture, poor key management, and insufficient monitoring. The attackers, often state sponsored groups like Lazarus, simply exploited the gaps that defenders left open.
But beyond the individual failures, these exploits reveal a deeper structural problem. Every bridge in this analysis maintained asset representations on multiple chains simultaneously: locked tokens on the source chain, minted tokens on the destination chain and trusted that validators would keep these representations synchronized. When attackers compromised those synchronization mechanisms, they minted unbacked assets on one chain while the other chain still showed funds as locked. The result was billions in phantom assets circulating through DeFi ecosystems.
This is the fundamental fragility of cross-chain bridges: distributed accounting across independent ledgers creates exploitable discrepancies under stress. Any architecture that maintains duplicate representations of the same assets across multiple chains inherits this risk, regardless of how many validators secure the bridge or how many audits the code passes.
The alternative is canonical accounting, where a single authoritative ledger serves as the source of truth for all positions, with cross-chain messages treated as instructions validated against that ledger rather than as authoritative state updates. Under this model, there is no second representation on another chain that can fall out of sync. If the messaging layer experiences delays or failures, transactions queue rather than creating phantom balances.
The lesson from 2022 is clear: bridge security cannot be an afterthought. The architecture itself must eliminate the accounting fragility that made these exploits possible. Before you bridge, ask whether the destination was designed to solve this problem at the infrastructure level.