In the first six months of 2025, hackers stole $2.47 billion from crypto protocols. That figure already exceeds total losses for all of 2024.
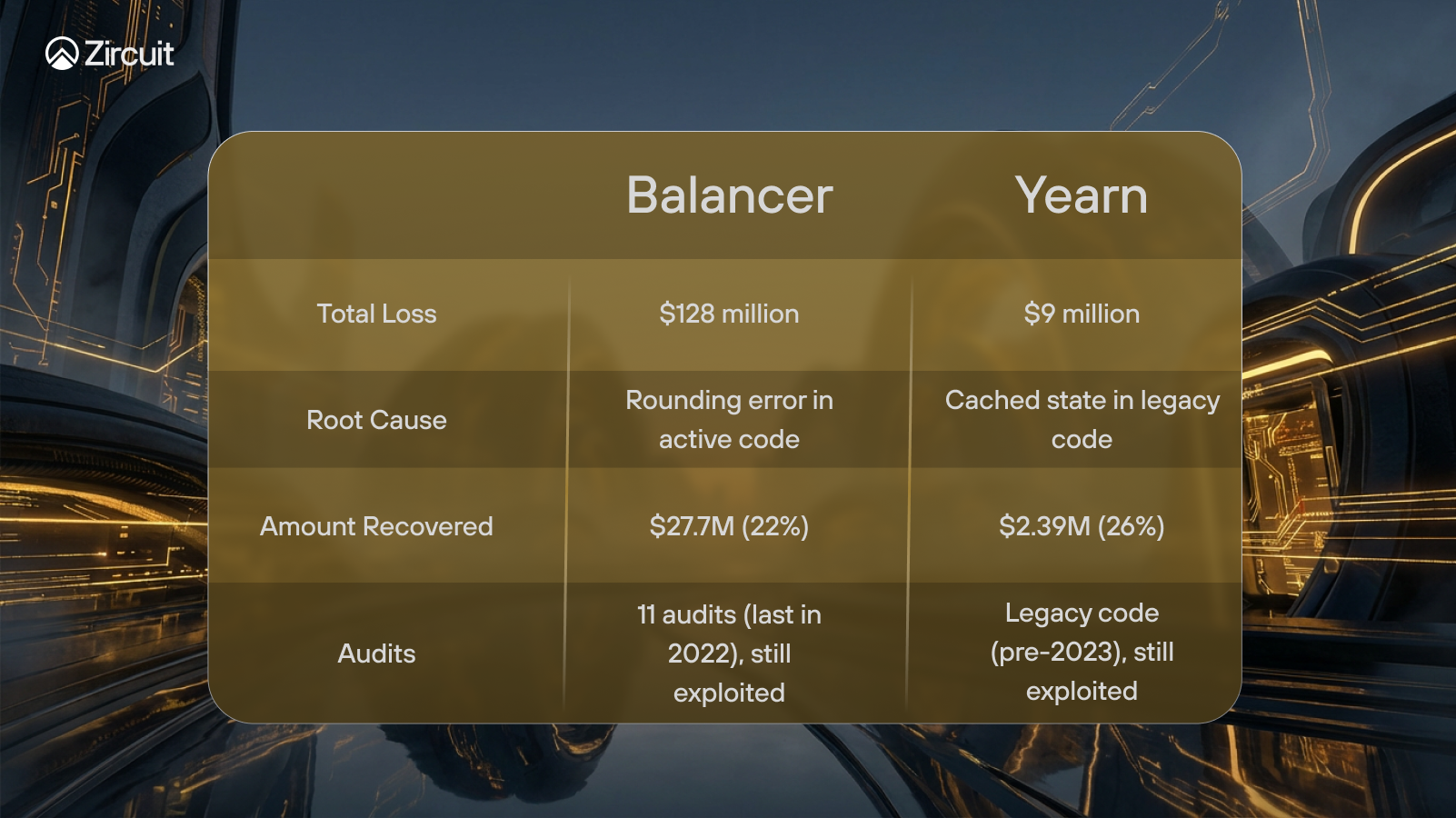
The rekt.news leaderboard tells a story that should concern every DeFi investor. Balancer now sits at position 21 after losing $128 million on November 3, 2025. Yearn Finance claimed position 119 after a $9 million exploit on November 30. These protocols had been operating for years. They had undergone multiple security audits. Balancer alone had eleven audits from four different firms, including formal verification from Certora.
None of it mattered when the attack came.
The vulnerability that drained Balancer had existed in the code since July 2021. A comment in the source code read: "the impact of this rounding is expected to be minimal." Four years and eleven audits later, that minimal impact became $128 million in losses across nine blockchain networks in under 30 minutes.
This is not a story about careless developers or amateur projects. This is a story about how even the most examined code can harbor flaws that remain invisible until someone decides to exploit them. The patterns behind these attacks are not random. They follow recognizable categories that investors can learn to identify before depositing funds.
The Balancer exploit began with a mathematical assumption that turned out to be catastrophically wrong.
At 07:46 UTC on November 3, 2025, an attacker began draining Balancer V2 pools across nine blockchain networks. Within 30 minutes, approximately $128.64 million had vanished through a vulnerability hiding directly beneath a comment where developers had written that rounding impact would be minimal.
The technical flaw resided in how Balancer handled token scaling during batch swaps. Solidity, the programming language used for Ethereum smart contracts, cannot process decimal numbers. Every calculation rounds down to the nearest integer. In most operations, losing a fraction of a token unit causes no meaningful harm. But the attacker discovered that pushing token balances to specific thresholds between 8 and 9 wei created relative precision losses approaching 10% per operation.
The attack weaponized a feature called batchSwap that allows multiple trades in a single transaction. The attacker executed 65 precisely calibrated swaps within one transaction, each one compounding the rounding error. The sequence followed three repeating phases: first, manipulate pool balances to reach the critical threshold; second, trigger swaps that artificially suppress the price of Balancer Pool Tokens; third, mint tokens at the suppressed price and immediately redeem them at full value.
Ethereum absorbed $91.5 million of the total losses. The remaining damage spread across Arbitrum, Base, Polygon, Optimism, Gnosis, Avalanche, and several Balancer forks including Beethoven X. Twenty seven protocols sharing Balancer V2 code inherited the same vulnerability.
Balancer V3 pools remained completely unaffected. The newer version had implemented bidirectional rounding that favors the protocol in every operation. The vulnerability existed only in V2 Composable Stable Pools where the fix had never been applied.
Security researchers noted something unusual about the attack contract. It contained console.log statements, debugging instructions typically removed from production code. This led to speculation that portions were generated using AI tools and deployed without proper review. The attacker funded the operation with 100 ETH from Tornado Cash, suggesting experienced execution despite the amateur code signatures.
Recovery efforts secured approximately $27.7 million, about 22% of total losses. Balancer TVL collapsed from $443 million to $186 million within 48 hours.
The Yearn Finance exploit three weeks later would prove that Balancer was not an isolated incident.
Three weeks after Balancer, another veteran protocol fell. On November 30, 2025, at 21:11 UTC, an attacker deposited 16 wei into a Yearn Finance contract. That deposit, worth approximately $0.000000000000000045, generated 235 septillion yETH tokens.
The number is difficult to comprehend. Written out, 235 septillion contains 24 zeros. The attacker used these artificially minted tokens to drain $9 million from connected liquidity pools within minutes.
The vulnerability exploited a state management flaw in legacy yETH code. When the pool supply reached zero, a cached storage variable called packed_vbs[] failed to clear properly. The attacker executed a precise sequence: first, repeatedly deposit and withdraw to poison the cached state; second, drain the pool to zero supply; third, trigger re-entry that activated bootstrap initialization using the stale cached values. The contract interpreted the corrupted data as legitimate and minted tokens without proper validation.
Check Point researchers titled their analysis simply: "16 Wei." The title captures the absurdity of how a deposit smaller than the smallest practical transaction could unlock millions in stolen funds.
Yearn V2 and V3 vaults remained unaffected. The vulnerable contract was legacy infrastructure that had been operating since earlier iterations of the protocol. Unlike Balancer, where the flaw existed in actively maintained code, Yearn suffered from technical debt that accumulated over years of protocol evolution.
The attacker moved quickly to obscure the trail. Within hours, 1,000 ETH worth approximately $3 million had been laundered through Tornado Cash. Recovery efforts managed to secure $2.39 million, roughly 26% of total losses, through intercepted funds that had not yet been mixed.
Two major exploits in the same month. Both targeting established protocols. Both exploiting edge cases that auditors had missed. The pattern was not new. The two attacks reveal how different vulnerabilities can produce similarly devastating results.
The exploits of 2025 follow patterns established years ago. Understanding historical attacks reveals that the vulnerability categories remain remarkably consistent.
On March 13, 2023, Euler Finance lost $197 million to a flash loan attack. The attacker exploited a function called donateToReserves that lacked proper liquidity validation. By manipulating collateral ratios through rapid borrowing and donating, the attacker created conditions where liquidations generated profit rather than protecting the protocol. In an unexpected turn, the attacker later returned all funds after negotiations, identifying himself only as "Jacob."
The GMX V1 breach on July 9, 2025, demonstrated a different category entirely. An attacker exploited a cross contract reentrancy vulnerability in the executeDecreaseOrder function. By hijacking the refund step during order execution, the attacker manipulated the global average short price from $109,515 to just $1,913, distorting GLP token valuations. This allowed minting tokens at $1.45 and redeeming them above $27, extracting $42 million from the protocol. The vulnerability had been introduced in 2022 as part of a fix for another bug. The attacker later returned $37 million after accepting a $5 million bounty.
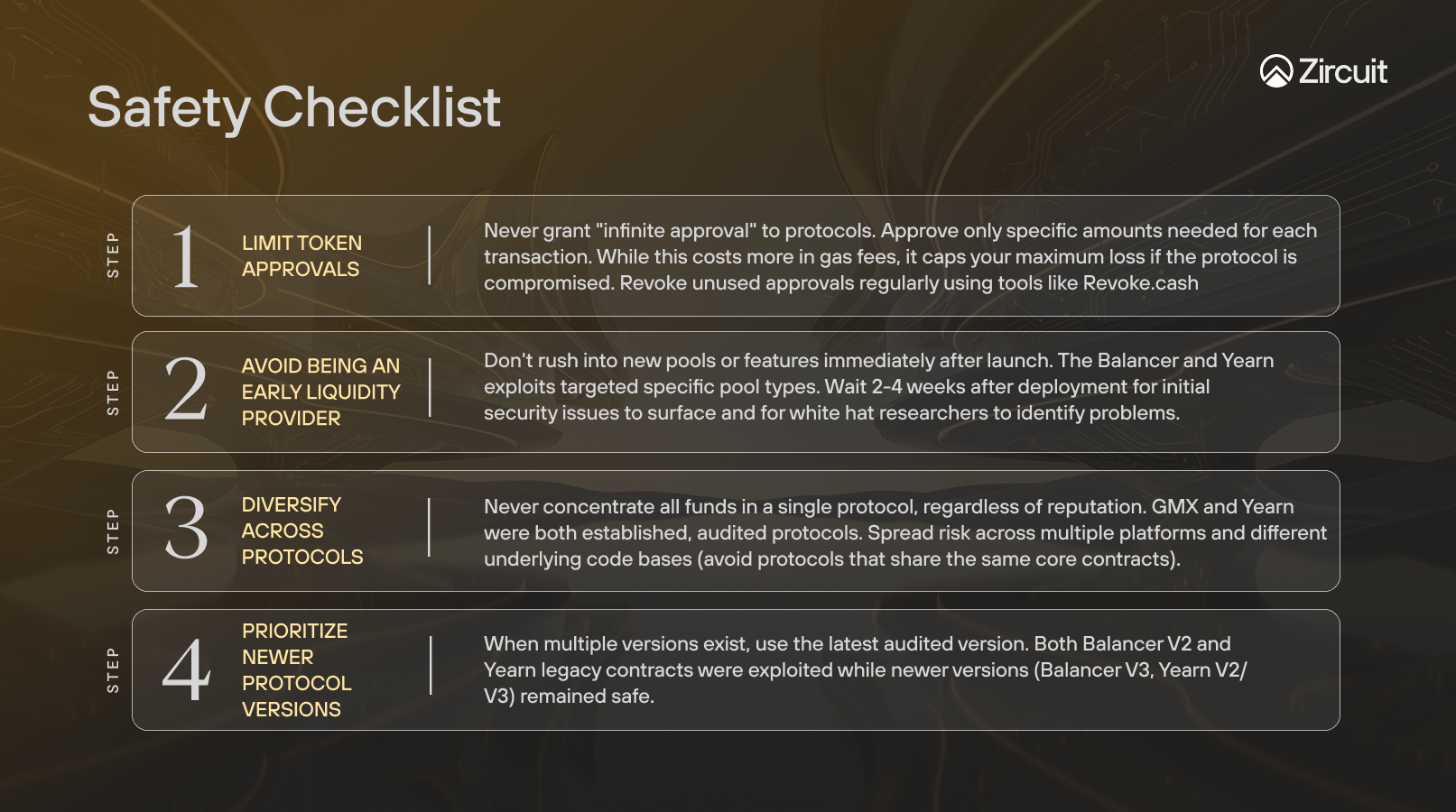
Four years earlier, the Furucombo hack on February 27, 2021, revealed the dangers of infinite token approvals. The attacker deployed an "evil contract" that tricked Furucombo into believing it was a new version of Aave V2. Once whitelisted, the malicious contract could drain tokens from any user who had previously granted Furucombo unlimited spending permissions. Unlike most DeFi exploits where the protocol absorbs losses, Furucombo's $14 million theft came directly from individual user wallets.
Three attacks. Three different technical vectors. Flash loans exploiting liquidity validation gaps. Cross contract reentrancy manipulating internal state. Infinite approvals enabling direct wallet drainage. These same categories reappeared in Balancer and Yearn. The technology evolves, but the fundamental weaknesses persist. Recognizing these patterns is the first step toward evaluating protocol risk.
Every major DeFi exploit falls into one of seven categories. Learning to recognize them transforms abstract security concerns into concrete evaluation criteria.
Rounding and Precision Errors occur when mathematical operations lose accuracy at extreme values. Balancer lost $128 million this way. Hundred Finance lost $7.5 million and Sonne Finance lost $20 million to similar flaws. Any protocol performing complex calculations on very small or very large numbers carries this risk.
Infinite Mint Attacks exploit logic flaws that allow token creation without proper backing. Yearn's $9 million loss originated here. So did Wormhole's $326 million breach, Harmony's $100 million exploit, and Qubit's $80 million drain. Protocols that mint tokens based on external inputs or cached states require careful scrutiny.
Flash Loan Attacks use uncollateralized borrowing to manipulate protocol conditions within a single transaction. Euler's $197 million hack exemplified this category. PancakeBunny lost $45 million and CREAM Finance lost $130 million through similar mechanisms. Protocols with price dependencies or liquidation systems face elevated exposure.
Reentrancy Attacks exploit the ability to repeatedly call a function before previous executions complete. GMX lost $42 million in July 2025 when an attacker hijacked a refund callback to manipulate token prices mid transaction. The Curve and Vyper incident in 2023 drained $69 million across multiple pools. Even The DAO hack of 2016, which prompted Ethereum's famous hard fork, used this same technique to extract $60 million.
Infinite Approval Exploits target users rather than protocols directly. Furucombo's $14 million hack in 2021 demonstrated this vector when an attacker tricked the protocol into whitelisting a malicious contract that drained tokens from every wallet that had granted unlimited spending permissions. Any user who clicks "approve" without setting limits becomes a potential target.
Access Control Failures bypass technical security entirely by compromising administrative keys. Ronin's $624 million theft required only five private keys. Private key compromises accounted for $1.7 billion in the first half of 2025, representing 69% of all losses. Protocols controlled by single keys or small multisig arrangements present obvious targets.
Oracle Manipulation feeds false price data to trigger favorable contract conditions. Mango Markets lost $115 million when an attacker manipulated token prices to borrow against inflated collateral. Bonq lost $120 million after an attacker staked just $175 worth of tokens to corrupt a price feed.
Seven categories. Billions in losses. The same patterns repeating across years.

Before depositing funds, investors can evaluate protocols against these specific risk vectors.
The Balancer and Yearn exploits expose a structural limitation in how the industry approaches security. Audits verify code at a single point in time. They check whether the logic is sound, whether known vulnerability patterns exist, and whether the implementation matches the specification. This is valuable but fundamentally incomplete.
The vulnerability that drained Balancer existed for four years across eleven separate audits. It was not that auditors were negligent. It was that the specific combination of conditions required to trigger the exploit: pushing token balances to precise thresholds during batch swaps, fell outside the patterns auditors were trained to detect. Novel attack vectors, by definition, cannot be caught by tools designed to find known ones.
This limitation has particular implications for any protocol that manages capital on behalf of depositors. A lending protocol, a yield vault, or any system that deploys user funds through external strategies does not just need its own code audited. It needs continuous evaluation of the transactions flowing through it, the health of the counterparties it interacts with, and the state of the contracts it depends on. Audits are a snapshot. Capital management is a continuous process.
The protocols that have survived longest in DeFi share a common trait beyond passing audits: they implement layered security that extends beyond code review. Real-time monitoring services like Hypernative, which detected the Balancer attack within two minutes, provide early warning capabilities that audits cannot. Timelocks on administrative functions give users time to exit before changes take effect. Circuit breakers that pause operations during anomalous activity limit damage when prevention fails. Formal verification adds mathematical rigor to critical functions.
No single measure guarantees safety. The goal is defense in depth, multiple independent layers that each catch what the others miss. Infrastructure designed with this philosophy from the beginning is fundamentally more resilient than infrastructure that bolts security onto an existing design.
Understanding attack categories enables practical security evaluation. Before depositing funds into any DeFi protocol, investors can assess specific indicators that correlate with risk.
Warning signs demand caution. Protocols controlled by single administrative keys or small multisig arrangements concentrate risk unnecessarily. Reliance on a single price oracle creates manipulation exposure. Legacy contracts that have not been updated alongside newer versions often harbor technical debt. Absence of timelocks on administrative functions allows instant malicious changes.
Positive indicators build confidence. Recent audits from reputable firms demonstrate ongoing security investment, though Balancer proves audits alone are insufficient. Active bug bounty programs with meaningful rewards attract security researchers who might otherwise become attackers. Real time monitoring services like Hypernative, which detected the Balancer attack within two minutes, provide early warning capabilities. Multisig arrangements requiring five or more signatures distribute control meaningfully. Timelocks on administrative functions give users time to exit before changes take effect. Formal verification, while not foolproof, adds mathematical rigor to critical functions.
Insurance options through providers like Nexus Mutual offer financial protection when technical measures fail. Coverage typically costs 2% to 10% annually depending on protocol risk assessment.
No single indicator guarantees safety. The goal is accumulating evidence that a protocol takes security seriously across multiple dimensions. Beyond evaluating protocols, investors can take concrete steps to protect their own wallets:
The patterns are clear. The tools exist. The choice belongs to each investor.
The $2.47 billion stolen in the first half of 2025 did not disappear through exotic new attack vectors. Rounding errors, infinite mints, flash loans, compromised keys, and manipulated oracles have been draining protocols for years. Balancer and Yearn joined a list that includes Euler, Ronin, Wormhole, and dozens of others.
Audits help but do not guarantee safety. Eleven security reviews could not prevent Balancer's collapse. Legacy code created Yearn's vulnerability. The protocols that survive long term treat security not as a checkbox but as foundational architecture.
This distinction matters when evaluating where to deploy capital. Some protocols bolt security measures onto existing systems after deployment. Others build security into their core design from the first line of code, with layered defenses that operate continuously rather than at a single point in time. The record is clear about which approach produces better outcomes.
The patterns are documented. The warning signs are identifiable. Security starts with knowing what to look for.