
In our previous articles, we examined the wreckage. Terra's algorithmic death spiral erased $40 billion in nine days. The contagion that followed brought down Three Arrows Capital, Celsius, and Voyager in a cascade of margin calls and frozen withdrawals. Stream Finance proved that even 2025 was not immune, with circular collateral arrangements unraveling across multiple protocols.
The pattern was consistent. Credit defaults on undercollateralized lending platforms erased approximately $90 million in aggregate. Security exploits claimed $2.47 billion in the first half of 2025 alone. Cross-chain bridges hemorrhaged over $2.5 billion in cumulative losses.

Protocols launched with audits and insurance and governance tokens, yet collapsed under stress their architectures were never designed to withstand. Now comes the harder question: what would infrastructure built to survive actually look like?
Institutional capital has been asking the same thing. According to Sygnum Bank's Future Finance report, no large institutional decision maker will allocate meaningful capital until legal and regulatory risks are fully resolved. The billions sitting on traditional finance sidelines are not waiting for higher yields. They are waiting for systems that do not break.
Zircuit Finance Vaults represents one attempt to answer that question. Founded by the security team behind Quantstamp, the platform addresses each documented failure mode with specific architectural responses: canonical accounting to prevent ledger fractures, institutional-grade vault architecture that intercepts risk before it reaches depositors, and institutional-grade strategy partners operating under regulatory oversight. What follows is an examination of how those responses work, and whether they deliver the survivability that institutional capital demands.
The question of who builds a protocol matters as much as what they build. In an industry where anonymous teams have vanished with billions, Zircuit's founding team represents a deliberate departure: academic researchers who spent years finding vulnerabilities in other people's code before writing their own.
Dr. Martin Derka earned his PhD studying algorithms and computational complexity before joining Quantstamp, where he audited smart contracts for projects managing billions in assets. Dr. Jan Gorzny completed his doctorate in Computer Science at the University of Waterloo, one of the world's leading programs for cryptography and formal verification. Together, they published 14 peer-reviewed papers and secured four foundation grants: three from the Ethereum Foundation and one from the ZCash Foundation.
This research background shaped a specific thesis: that security cannot be bolted on after deployment. It must be embedded at the infrastructure layer, before risk ever reaches depositors. That thesis became Zircuit Finance Vaults, a platform engineered from the ground up to eliminate the counterparty opacity, accounting fragmentation, and exploit vectors that destroyed its predecessors.
The founding team's background also attracted institutional backers who understood the approach. YZiLabs, Dragonfly, Pantera, and Binance Labs all participated in funding rounds, providing both capital and the kind of due diligence scrutiny that validates architectural decisions before they are tested by markets.
Yield generation is only as reliable as the counterparties producing it. The collapses we documented in previous articles shared a common thread: opaque relationships with unregulated entities that promised returns they could not sustainably deliver. Zircuit Finance Vaults selected strategy partners based on the opposite criteria: verifiable track records, regulatory oversight, and institutional infrastructure.
Monarq Asset Management brings quantitative trading expertise developed across traditional and digital markets. CEO Shiliang Tang studied at MIT before trading volatility at Merrill Lynch and UBS. He founded LedgerPrime in 2017 and scaled it to $400 million in assets under management by 2022. In June 2025, FalconX acquired a majority stake in Monarq, a distinct entity founded by former LedgerPrime team members, integrating its delta neutral strategies with institutional-grade prime brokerage services.
Forteus, operating under the Numeus Group umbrella, represents the traditional finance pedigree that institutional allocators recognize Forteus operates under FCA regulation in the United Kingdom. The firm maintains offices in Zug, London, New York, and Mauritius. Numeus Group is led by CEO Nobel Gulati, formerly CEO of Two Sigma Advisers.
FalconX serves as the execution and prime brokerage layer connecting these strategies to markets. The platform holds an $8 billion valuation and maintains CFTC registration as a swap dealer, providing the regulatory standing that institutional compliance departments require before approving counterparty relationships.

This partner structure addresses the counterparty opacity that destroyed earlier yield platforms. Rather than routing capital through anonymous protocols or unverified fund managers, the vault architecture connects depositors to regulated entities with auditable operations and established reputations they would risk destroying through misconduct.
The bridge exploits we examined in earlier articles revealed a structural weakness that audit reports consistently missed: when asset representations exist on multiple chains simultaneously, stress conditions create opportunities for accounting discrepancies that attackers can exploit. The protocol addresses this vulnerability through an architecture that eliminates distributed ledger fragmentation entirely.
The hub and spoke model establishes a single canonical accounting chain as the authoritative source of truth for all vault positions. Deposits flow inward from supported networks, strategy allocations execute through regulated partners, and yield distributions flow outward to depositors. At every stage, the canonical ledger maintains the definitive record of who owns what. There is no secondary representation on another chain that could fall out of sync during network congestion or bridge delays.
Cross-chain communication operates through LayerZero messaging infrastructure, but the architecture treats these messages as instructions rather than authoritative state updates. When a user deposits USDC from Ethereum, LayerZero transmits the deposit instruction to the canonical chain, which validates the message, updates its ledger, and only then considers the deposit complete. The user's position exists in exactly one place.
This design directly counters the failure mode that destroyed cross-chain bridges holding billions in user funds. Protocols like Wormhole and Ronin maintained asset representations across multiple chains, trusting that validators would keep these representations synchronized. When attackers compromised those synchronization mechanisms, they minted unbacked assets on destination chains while the source chains still showed funds as locked.
The vault layer adds real-time exposure reporting that shows depositors exactly how their capital is allocated across strategy partners at any moment. Combined with whitelisted counterparty restrictions that limit which entities can receive capital deployments, this transparency addresses the opacity that allowed earlier platforms to concentrate risk without depositor knowledge.
The architecture does not eliminate all risk. Strategy partners can still underperform, market conditions can compress yields, and smart contract vulnerabilities may exist despite audits. What canonical accounting eliminates is the specific category of cross-chain accounting exploits that have historically produced the largest single-incident losses in decentralized finance.
The collapses we have examined throughout this series did not fail randomly. They failed through specific, identifiable mechanisms that recurred across protocols, market conditions, and years.
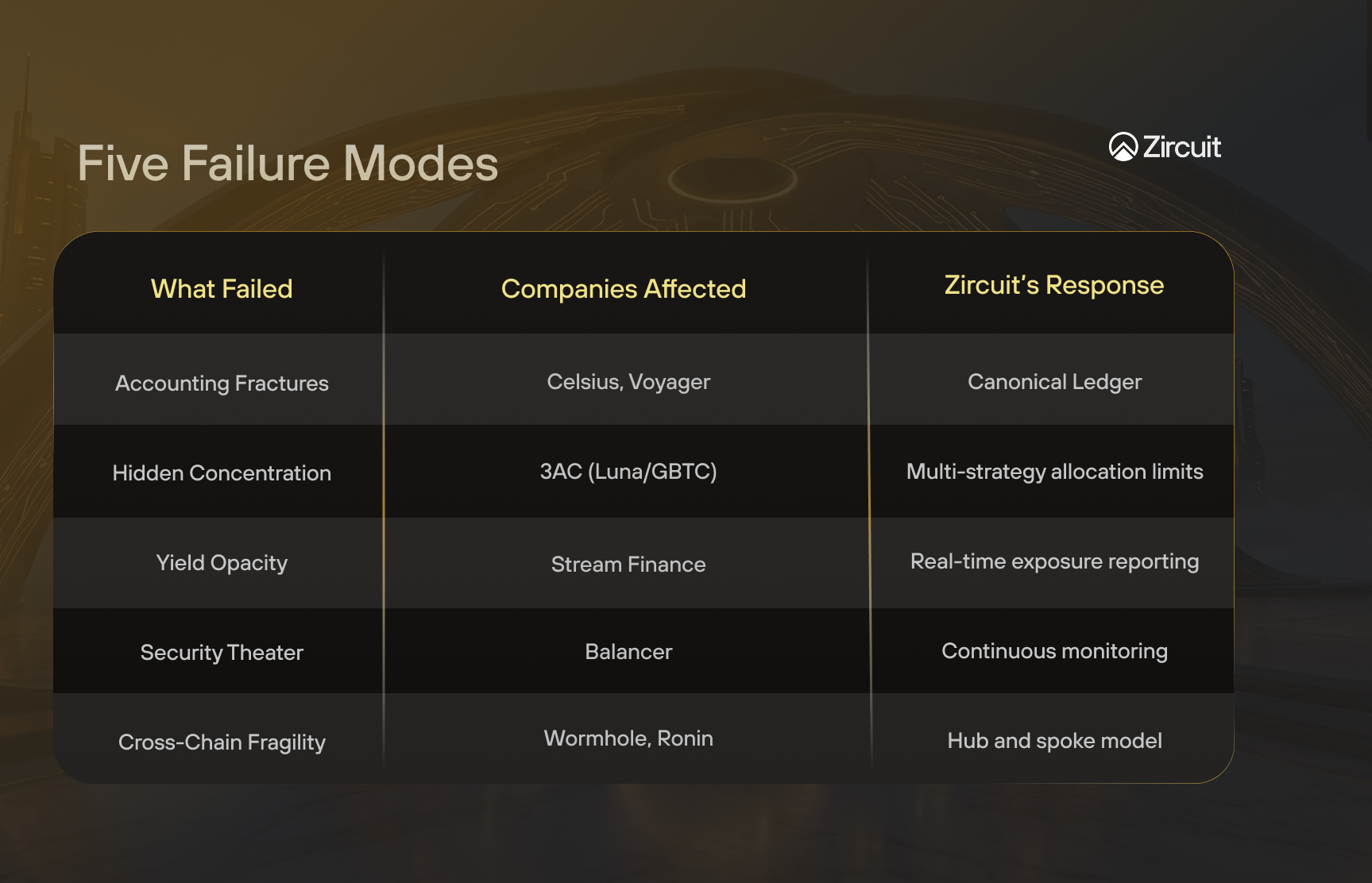
The vault system structures its architecture around preventing these documented failure modes rather than assuming they will not happen again.
Accounting fractures under stress. When Celsius and Voyager faced withdrawal pressure, their internal accounting could not reconcile positions fast enough to meet redemptions. The canonical ledger model maintains a single authoritative record that eliminates reconciliation delays between fragmented systems.
Concentration disguised as diversification. Three Arrows Capital appeared diversified across dozens of positions, but excessive exposure to Luna and leveraged GBTC trades created hidden concentration. Zircuit Finance distributes capital across multiple strategy partners operating different methodologies, with allocation limits preventing any single counterparty from accumulating outsized exposure.
Opacity in the yield engine. Depositors on failed platforms discovered too late that their capital funded uncollateralized loans to insolvent borrowers. Real-time exposure reporting shows depositors exactly where their funds are deployed, while whitelisted counterparty restrictions ensure capital only flows to pre-approved, regulated entities.
Security theater versus layered defense. Balancer underwent eleven separate audits before losing $128 million to a rounding error none of them caught. Audits verify code at a point in time but cannot prevent novel attack vectors. The vault architecture implements multiple layers of runtime protection beyond conventional audits: continuous monitoring, circuit breakers, and counterparty health checks that evaluate risk on an ongoing basis rather than at a single point in time.
Cross-chain fragility. Bridge protocols lost over $2.5 billion when attackers exploited synchronization failures between chain representations. The hub and spoke architecture treats cross-chain messages as instructions validated against the canonical ledger rather than authoritative state updates, eliminating the double-spend vectors that destroyed earlier bridges.
Each architectural choice maps directly to a documented failure. The question for depositors is whether these responses adequately address the risks they care about most.
Intellectual honesty requires distinguishing between the risks this architecture addresses and the risks it cannot.
The failure modes documented throughout this series fall into two distinct categories. The first is architectural risk: cross-chain accounting fractures, opaque counterparty relationships, circular collateral dependencies, and the absence of real-time monitoring. These are design failures. They produce sudden, catastrophic losses, the overnight collapses that erase 90% of value in 48 hours. Canonical accounting, regulated counterparties, and real-time transparency are direct, structural responses to these specific failure modes.
The second category is market risk: strategy underperformance, yield compression during adverse conditions, and the inherent uncertainty of deploying capital in volatile markets. No architecture eliminates these risks. If Monarq or Forteus makes a bad trade, canonical accounting will not reverse the loss. If market conditions deteriorate, yields will decline regardless of how transparent the reporting is.
The critical difference is the character of the risk. Architectural failures are sudden, total, and often irrecoverable, Terra went from $40 billion to zero in nine days. Market risk is gradual, bounded, and manageable through diversification, position limits, and the ability to exit before losses compound.
The vault architecture is designed to ensure that depositors face market risk - the kind that can be understood, monitored, and managed - rather than architectural risk, the kind that produces overnight catastrophe with no warning and no exit. This is not a guarantee of returns. It is a guarantee that the specific categories of failure that have historically destroyed the most capital have been addressed at the infrastructure level.
Whether that distinction proves sufficient will only become clear under continued market stress.
The regulatory environment that kept institutional capital on the sidelines is shifting. MiCA took effect in December 2024, establishing the first comprehensive framework for digital assets in the European Union. The OCC issued Interpretive Letter 1183 in March 2025, explicitly permitting national banks to custody digital assets. The GENIUS Act passed in July 2025, creating federal standards for stablecoin reserves and issuer licensing.
Institutional behavior is following regulatory clarity. According to the EY and Coinbase institutional survey, 86% of institutional investors now hold digital asset exposure, and 75% plan to allocate to DeFi protocols within two years. In September 2025, Société Générale's digital asset arm deployed capital through Uniswap and Morpho, marking the first major European bank to execute DeFi strategies directly.
This convergence creates demand for infrastructure that meets institutional requirements: regulatory compliance, counterparty transparency, and architectural resilience. Platforms built for retail speculation cannot satisfy the due diligence processes that compliance departments require. The capital is ready. The question is whether the infrastructure exists to receive it responsibly.
The failures we documented across this series share a common lesson: yield without survivability is not yield at all. It is leveraged exposure to systems that have not yet broken.
Zircuit Finance Vaults represent an architectural response to that lesson. Canonical accounting eliminates the cross-chain fragmentation that enabled billion-dollar bridge exploits. Regulated strategy partners operating under FCA and CFTC oversight, backed by firms with institutional pedigrees built over decades replace the opaque counterparties that defaulted on promises they could not keep. Real-time exposure reporting replaces the information asymmetry that left depositors discovering risks only after losses materialized.
These are structural responses to documented failures, not marketing claims. Whether they prove sufficient will only become clear under continued stress. Markets will test the architecture. Attackers will probe for vulnerabilities the designers did not anticipate. The difference is that the platform enters that testing period having studied what destroyed its predecessors and built specifically to avoid repeating those failures.
The honest assessment is this: the vault architecture eliminates the categories of risk that have historically produced the largest and most sudden losses in DeFi: cross-chain accounting exploits, counterparty opacity, circular collateral, and concentration risk. It does not eliminate market risk. Strategies can underperform. Yields can compress. Capital deployed in volatile markets carries inherent uncertainty.
For institutional allocators, the relevant question is not whether all risk has been eliminated. It never can be. The question is whether the risks that remain are the kind that can be understood, monitored, and managed, rather than the kind that produce overnight catastrophe. That is the standard the architecture was designed to meet.